

Trusted by:




Assess your business' vulnerabilities before hackers do
With thousands of companies facing cyber attacks, protecting your organisation is crucial. Our external vulnerability assessment will enable your business to stay safe and secure by uncovering potential weak points.
Don't wait - act now and safeguard your business from threats.
About our vulnerability assessment tool
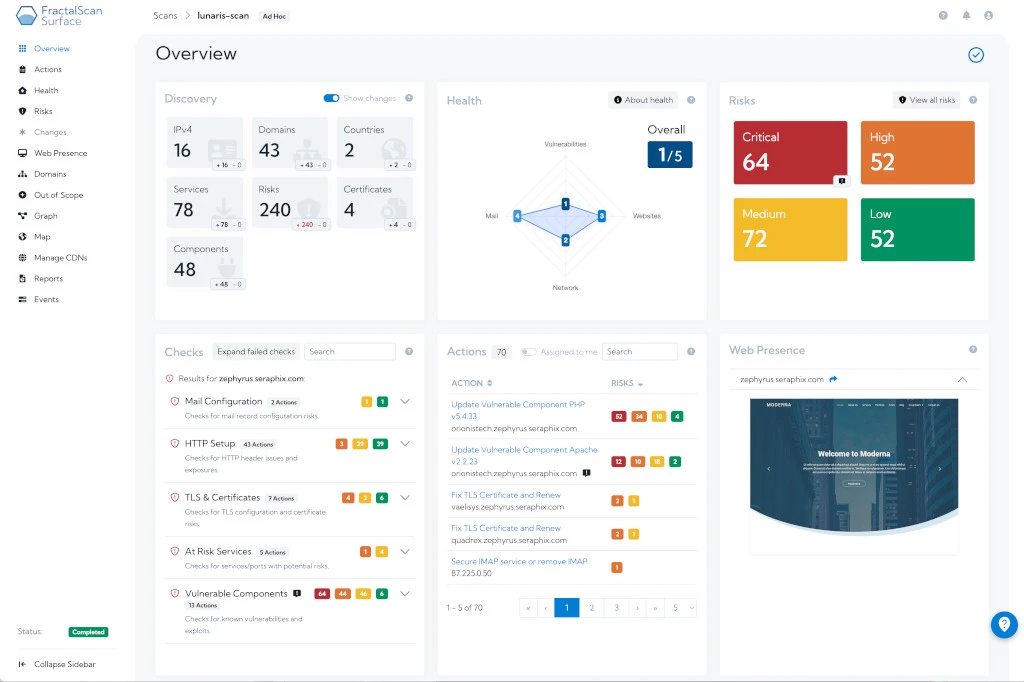
Built by our cyber security experts, FractalScan Surface is a vulnerability assessment tool designed to conduct comprehensive evaluations of your online infrastructure, identifying vulnerabilities. Our platform runs thorough scans of all your online assets and generates an in-depth report highlighting your potential risks and actionable guidance for remediation, allowing you to resolve any weaknesses before hackers exploit them.
Our user-friendly interface makes it easy to use, with automated alerts and reporting functions, making it the ideal tool for organisations of any size, from SMEs to large enterprises.
Make your business cyber secure with FractalScan’s external vulnerability assessment

What is a vulnerability assessment?
A vulnerability assessment is the process of identifying, quantifying, and prioritising vulnerabilities in an organisation's network, systems, applications, and infrastructure.
This assessment helps businesses to understand their security posture and evaluate the potential impact of a security breach.
A vulnerability assessment can be done manually or with automated tools, such as vulnerability scanners or penetration testing.
The primary goals of a vulnerability assessment are to:
- Identify vulnerabilities that may expose the business to cyber threats or data breaches.
- Evaluate the severity and potential impact of each vulnerability on the organisation.
- Prioritise vulnerabilities for remediation based on risk and criticality.